Introduction
This lesson will cover IP address management and a topic everybody loves, subnetting. There will be information in this lesson that will help identify network and host portions of an IP address. Lastly, this lesson will explain how to calculate the number of host and subnets needed on a network.
Lesson Objectives
By the end of this lesson, you will be able to:
1. Calculate available hosts within Internet Protocol (IP) address range.
2. Describe purpose of the subnet mask and its relationship to Classless Inter-Domain Routing (CIDR).
3. Explain subnetting and calculate subnets.
4. Explain “ANDing” and what it is used to identify.
IP Address Management
It is important to be able to identify the Number of Hosts per IP Class. The equation for calculating how many hosts can be in each IP Address class is:
2n – 2 = Numbers of available host.
Refer to the equation and consider: Why subtract two? You should subtract two because:
- The first bit is reserved to identify the network (i.e. 129.0.0.0), Network address.
- The last bit is reserved for the Broadcast address (i.e. 129.255.255.255).
The network address identifies which network a host resides on. The broadcast address is used to reach every node within the specified range. This is typically described as a Point to multipoint.
If we wanted to send a message to everyone within a specified range, we would use the broadcast address. When attempting to reach one host on the network instead of many, this would be referred to as Point to Point or a Unicast address.
Review the chart provided below which includes the class, number of host bits and number of hosts. Working the equation 2n – 2, for the Class C Address range, you would get: 28 – 2 = 256 – 2 = 254. Review the chart for details.
| Class | Number of Host Bits | Number of Hosts |
| A | 24 | 16,777,214 |
| B | 16 | 65,534 |
| C | 8 | 254 |
Subnet Masks
Subnet masks are used to identify which bits in an IP address are used to represent the network ID portion. A subnet is a way to break up an IP address range into several different/separate sub networks.
Some network administrators have a need to separate hosts or segment a network. They will often borrow host bits and add them to the network portion of an IP address, creating a subnet. The octets with 255 have their network bits reserved. See chart below.
| CLASS | Default Subnet Mask |
| A | 255.0.0.0 |
| B | 255.255.0.0 |
| C | 255.255.255.0 |
Just as with the subnet mask, Classless InterDomain Routing (CIDR) can be used to specify the Network ID portion of an IP address. CIDR commonly pronounced “cider” uses a notation after the IP address that denotes which bits are reserved for the Network ID (i.e. 190.12.100.6/16).
CIDR is also known as “classless” notation due to being able to recognize the IP address class by the ‘/x’ notation. Review the following information and the chart which will help guide you in determining class address:
Class A: 8 bits reserved for the Network ID
Class B: 16 bits reserved for the Network ID
Class C: 24 bits reserved for the Network ID
Note: It is important to review what was covered in the subnet mask part of the lesson and how it ties to Network ID as 8 bits of an IP address = 255, 16 bits = 255.255, 24 bits = 255.255.255.
| CLASS | Classless Notation |
| A | 25.131.54.10/8 |
| B | 175.88.19.100/16 |
| C | 193.234.190.50/24 |
What is Subnetting?
Subnetting occurs when a network is divided into two or more networks. A corporation will have various departments that will need access to the network. Having them all on the same network segment can reduce performance and security.
Subnetting can be hard to understand but as an example think of a tall building where each floor represents a subnet. Each floor is part of the building, yet each floor is separated from the other floors.
You can also think of Subnetting as dividing a pie so that each section of the pie is separated from the other. Another example would be when the law department may want the computers in their department on a different subnet.
The Social Media department may require high network usage and a Network Administrator may decide to place this department on a separate subnet.
Creating a Subnet
In order to create a subnet, host bits are borrowed then added to the network portion of an IP address for use.
For an illustration of how to create a subnet, review the following example.
Create a Subnet Example: Company A
Company ‘A’ consists of six different departments. These departments need to be on their own subnet within the 172.20.0.0 network or “pie”. For six different departments, or subnets, in this case you would need to borrow 23 = 8 bits.
- If ‘0’ is chosen for x then you do not want to split up the IP address (the pie) into subnets. When subnetting you choose the Most Significant bits of the host range. Company ‘A’ can have an Accounting dept., Human Resource dept., Legal dept., Information Technology dept., Maintenance dept., and Shipping dept. Why 2 to the 3rd? You would only need 6. Break down 2 to the 1st, 2nd, etc.
- Borrowing the three most significant bits from the host portion gives the following:
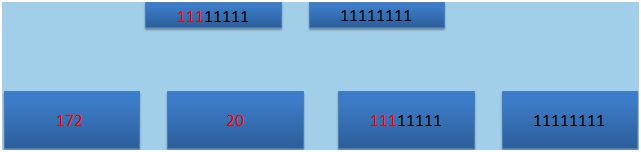
Figure 1 Example Company A: The red numbers represent the Network ID’s and the black numbers represent the remaining host bits available for use. The most significant bits are 2^7, 2^6, 2^5.
Completing all the possible 1 and 0 combinations between the three bits you would get the possible subnets. Review the chart (Eight (8) Subnets Created by Borrowing Three Host Bits), and Figure 2.
Eight (8) Subnets Created by Borrowing Three Host Bits
| 128 Address | 64 | 32 | Host Bits | Subnet |
| 0 | 0 | 0 | 00000.00000000 | 0 |
| 0 | 0 | 1 | 00000.00000000 | 32 |
| 0 | 1 | 0 | 00000.00000000 | 64 |
| 0 | 1 | 1 | 00000.00000000 | 96 |
| 1 | 0 | 0 | 00000.00000000 | 128 |
| 1 | 0 | 1 | 00000.00000000 | 160 |
| 1 | 1 | 0 | 00000.00000000 | 192 |
| 1 | 1 | 1 | 00000.00000000 | 224 |
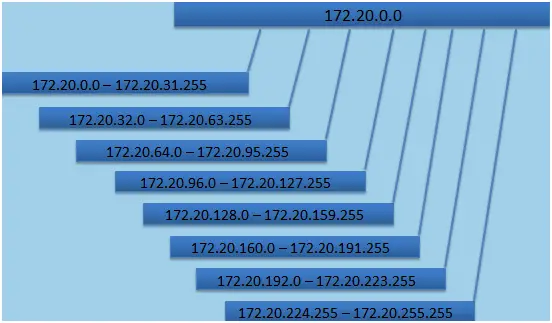
Figure 2 Representations of Subnets and their IP Ranges
Additional Subnet Equation
Another equation can be used to calculate the number of usable host per subnet. The equation is 2(y-x) – 2, where y is the number of host bits for the class of IP address and x is the number of borrowed bits.
Using the example of 172.20.0.0, where we borrowed 3 host bits – 2(y-x) – 2 = 8190. The minus (-) 2 in our equation is to account for the network address and the broadcast address for the subnets. When creating subnets it is important to consider the actual number of usable host.
Just as there is a default subnet mask for the IP address range, there is also one needed for the new subnet range.
Determining a Subnet Mask
To determine this new subnet mask you would complete the following:
- Take the default subnet mask for the class of IP address that was sub netted. In this case, Class B would be 255.255.x.x.
- Add to the default subnet mask the number of bits borrowed to create the subnets. In this case, the three (3) Most Significant bits (MSB’s) from the host range. These three bits add up to 224 (128+64+32). (i.e. 255.255.111xxxxx.xxxxxxxx)
- The new subnet mask would be 255.255.224.0.
If subnetting is still unclear, please watch The Basics of Subnetting IPv4 (6:34).

ANDing
ANDing is used to determine the network a data packet is destined for. A Router uses the ANDing process to decide whether to forward a data packet outside the network or internally. ANDing the destination IP address and the subnet mask identifies the network address a packet should be routed to.
The ANDing process involves what is called an AND operation. The following table describes this process. The only time you count the bit is when you have a 1 in the subnet mask that corresponds to a 1 in the IP address.
| Subnet Bit | IP Address Bit | = |
| 0 | 0 | 0 |
| 0 | 1 | 0 |
| 1 | 0 | 0 |
| 1 | 1 | 1 |
Please review the explanation and Figure 3 below which illustrates the ANDing process.
- IP address 192.168.20.3 (11000000. 10101000. 00010100. 00000011)
- Subnet Mask 255.255.255.0 (11111111. 11111111. 11111111. 00000000)
The resulting row from the AND operation is 192.168.20.0. This identifies the network address.
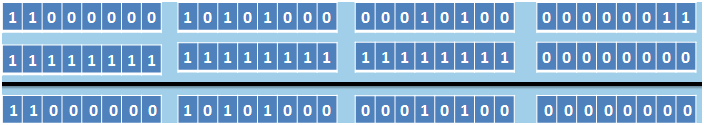
Figure 3 ANDing Process
Summary
In this lesson, you learned how to select the IP address range needed for your organization. Attributes of IP addresses and how they can be segmented to represent network boundaries (subnetting) were discussed.
In this lesson you gained an understanding of the process of ‘ANDing’ which is used to determine whether or not a data packet belongs on the network.