Introduction
In this lesson you will be introduced to tools and software used to manage a network. Often a need will arise to identify when a cable goes bad or a router/switch is not functioning as it should. A network administrator will use these tools and software to determine where the issue is to quickly resolve or physically fix the issue.
Lesson Objectives
By the end of this lesson, you will be able to:
- Identifying the appropriate hardware and software tools to troubleshoot network connectivity issues.
- Understand how to analyze network traffic and logs of network systems.
Network Media Testing: Common Tools

Multimeters and toner generators are common tools used for network media testing. Multimeters are used to test voltage, current and resistance in cables. Cables with high resistance measurements are considered faulty. A short or break in the cable are common examples where the resistance measurements will be high.
To learn the basics of how to use a multimeter watch Using a Multimeter Part 1 (9:23).

Toner generators and probes are used to identify cables that may be mixed up or lost. When a cables path is outside of a technician’s view (i.e. behind a wall or across ceiling space) toner probes and generators are used to locate cables.
To learn how to use a tone generator, watch the following video: Tone Generator and Probe (3:11).

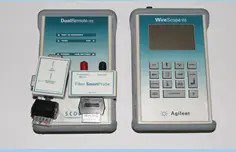
Cable Testers
A cable tester, simply, test cables and aids in troubleshooting issues involving the physical media. As discussed in previous chapters, there are distance limits set on the type of media used (i.e. CAT 6 cable can only span 100 meters). “Cable tester” is a broad term with alternative names and functions.
When troubleshooting there are several issues involving the physical media that need to be considered:

- the length of the cable
- a break in the cable
- the location of the cable
- a short
- incorrect cable configuration
- noise or interference
To gain a better understanding of how this tool works watch, Cable Tester (7:43).

Additional types of cable testers include:
- Continuity testers are commonly referred to as multimeters. Multimeters are used to test voltage, current and resistance in cables.
- Butt set will connect to the telephone transmission wires and test for a dial tone or signal; on the line.
- Cable certifiers do the same job as a cable tester; however, cable certifiers are often more advanced than an ordinary cable tester.
They do the job of testing the cable for resistance, length, and proper termination, all on one device. Due to the advanced features of a cable certifier, it is an expensive piece of equipment to purchase. Prices can be greater or equal to $4000.00. For more information on a specific tool used to test copper and Ethernet cables watch the following video: JDSU Test –
UM NT1150 ValidatorPRO Ethernet Speed Certifier (3:34).

- Time Domain Reflectors (TDR) and Optical Time – Domain Reflectors (OTDR) are cable testers that offer more abilities than the lower priced cable testers. Often they can tell where the break in the cable is and the required length of the cable.
Physical Media Tools
This lesson has identified and discussed various physical media tools used in network management. Here are a few more commonly used tools: a loopback plug, a punch down tool, and crimpers.
- A loop back plug is used for testing NIC configuration and health. It is inserted into the host’s NIC port (RJ-45). Outgoing communications hit the loopback plug and are redirected back to computer (host) for testing.
- A punch down tool is used to make sure the twisted wire is properly connected a plug or patch panel. The plug and patch panels have metal connectors that the copper wire must make a clean connection with. The punch down tool is used to ensure the copper wire and metal connectors on the plug and patch panel make a solid connection.
- Crimpers are used to terminate telephone, UTP and STP cables to their designated plug types (RJ11, RJ45).
Network Environmental Tool
Environmental monitoring describes when a physical appliance is used to check the temperature, humidity and power settings of attached systems. This type of tool is used to ensure availability or uptime. Environmental monitors also alert administration to flooding, smoke, fire, air flow and other conditions that may affect computational systems.
Software Network Testing: Connectivity and Data Collection
Review the following types of connectivity and data collection opportunities that are available which also provide options for software network testing.
Protocol Analyzer: A common protocol analyzer is packet sniffer such as NetMon, Wireshark, and EtherAPE. Packet sniffers are used to capture data traffic traveling across the media attached to a machine. So if you ran a packet sniffer on a computer on Network ‘A’, you would be able to see all the traffic on Network ‘A’. This tool can be used to determine why communication between two systems fail, errors will be seen in the packet capture. A computer flooding the broadcast domain with malformed packets can be identified and taken offline to restore network functionality.
Throughput testers: Throughput testers such as Iperf, netperf, and Ttcp are used for bandwidth measurement. Speed Test is an example of a Throughput Tester. Network technicians use tools like Speed Test to verify they are receiving the network bandwidth promised from their ISP.
Connectivity Software: Connectivity software allows administrators to troubleshoot and fix connectivity issue whether local or remote. Examples include remote desktop (RDP), virtual network computing (VNC), and LogMein.
Network Application Programs
It is important to have an understanding of the following network application programs.
- PING is used to test communication between two hosts and relies on the ICMP protocol. The host that receives the PING command will reply back to system that sent PING request or host to host activity. PING can be used to test latent connections and availability of some Internet-based services. PING is often blocked by network administrators to deter users from “sensing” their network assets.
- ‘Tracert’ is a windows command and ‘traceroute’ is a Linux command; used to trace path between two hosts. Each router the packet passes through, from host to destination, is printed out in the terminal or DOS prompt.
- Nslookup is a command that tries to resolve a fully qualified domain name (FQDN) into an IP address by querying a Domain Name Server (DNS) server.
- Dig is a DNS diagnostic tool used in Unix and Linux systems.
- Ipconfig and ifconfig are windows commands and Linux commands respectively used to gather information from the NIC such as IP address, physical address, and DNS addresses. Linux systems use this command to enable or disable the NIC itself and on a windows system there are various switches that enable NIC management.
- Netstat can be used to resolve port conflicts and determine if ports are listening or not. It can also be used to display detailed information on the process using the port and its associated protocol.
- Route is a windows command that can be used to display local system routing information and add additional routes. This is not to be confused with the routing table on a router; this is specific to the Windows host. Commands include route print and route add.
- Nbstat is only used on Windows systems. It can be used to look up NetBIOS names and when encapsulated with the TCP/IP protocol, resolve NetBIOS into IP address.
Network Monitoring
Simple Network Management Protocol (SNMP) is used to manage and obtain data from network devices. SNMP protocol uses Management Information Base (MIB) which is a collection of standard objects that are used to obtain configuration parameters and performance data on a networking device.
In order to capture data from the networked device, SNMP must be configured on the device itself. The network management console polls the various network devices which have an agent that collects data on device operation and performance. Networking monitoring tools such as Nagios and SCOM use SNMP to gather information on network devices.
| Key Facts
SNMP
SNMPv3
|
Log Analysis
General logs track configuration changes and windows service status, they can be combined with other log types and filtered for a more effective log analysis.
Many computers and servers keep a log of events that take place on the system. On a windows system these events can be seen through the Event Viewer. Some of the common logs located within event viewer include: System Logs, Security Logs and Application logs. There are three types of events that system logs record: Informational, Warnings, and Errors. In Unix and Linux systems the syslog records all system errors, however it does not alert you to problems (unlike Windows System Log).
History logs contain a collection of event logs including security, application, and system over a long period of time such as one year. Moreover, history logs are sometimes archived, compressed and saved, for later review.
Additionally, Microsoft has a tool called Performance Monitor also known as Perfmon which helps to monitor network and system performance.
Traffic Analysis
Traffic analysis should be done on an ongoing basis to ensure that bandwidth and throughput are effectively managed. When managing a network, the normal level of data traffic should be measured (baseline). Once a baseline can be established, different software and appliances can be employed to monitor increased traffic through the network. Finisar is a company that creates traffic analysis tools for area networks.
Often a network operations center (NOC) or network administrator may want to alter how data flows through the network to provide timely delivery and high performance. This method helps provide a quality of service on the network. Traffic filtering, limits what kind of data traffic can pass from one part of the network to the other.
Another way in which network performance can be managed is by shaping the traffic on the network, known as, traffic shaping. Traffic shaping involves altering the characteristics of packets and data to manage the amount of traffic on the network. Data may be injected into data packets so routers will not process them. Often low priority data packets like PING are delayed while VoIP data packets have an increased priority and are forwarded.
Network Forensics
Network sniffer and forensic appliances offer a wide breadth of functionality. An appliance, Network Time Machine, from Fluke Networks for instance, can capture traffic from several interfaces, represent the data graphically, and store this data for review at a later time.
It can also serve the purpose of a packet sniffer, network sniffer, protocol analyzer, and traffic analyzer all in one. The advantage with such network appliances is that they also make recommendation on how to improve network performance. Often this product is used to evaluate network health.