Networking is important in today’s world to everyone in business and at home. This lesson explains how a user configures their desktop to connect to other computers on a home network, a business network or the Internet.
Windows Networking
Before a computer can connect to any network, its Network Interface Card (NIC) must be configured with three pieces of information:
- A unique IP address that identifies the computer
- A subnet mask to find the network address
- A default gateway which is the IP address of the router the computer uses to access the Internet
From the Network Connections window, the IP settings can be configured on the NIC for IPv4 and IPv6. Right-click the network connection and select Properties. Select the appropriate Internet protocol version, and click on the Properties button.
Although it is not required, a DNS address is usually added to allow the computer to look up IP addresses for a given name.
Other common settings are:
- Duplex – half (in one direction only) or full (in both directions)
- Speed – 10, 100, 1000 Mbps
- Wake-on-LAN –an Ethernet networking standard that allows a computer to be turned on or awakened remotely
- Quality of Service (QoS) – specifies a guaranteed level of delivery including availability, bandwidth, delay, and error rate.
Network Connections
After configuring the addressing on a computer, it can connect to various networks. Previous lessons introduced the Local Area Network (LAN) and the Wide Area Network (WAN). Many devices including phones, tablets and computers can also connect to a Wireless Wide Area Network (WWAN). A WWAN allows a user with a mobile device or a laptop and a WWAN card to access the Internet or a VPN. Common cellular network standards include:
- LTE – Long-Term Evolution
- WiMAX – Worldwide Interoperability for Microwave Access
- UMTS – Universal Mobile Telecommunications System
- CDMA – Code Division Multiple Access
- GSM – Global System for Mobile
- CDPD – Cellular Digital Packet Data
These standards may vary by wireless service provider.
Network Location
The first time a user connects to a network, they can choose a network location. The firewall and security settings are then automatically set according to the network location selected.
The three types are:
- Home networks are for personal or private networks where the people and devices on the network are trusted. Network discovery is turned on, which allows the computer to see other devices and computers on the home network and allows the computer to be seen by other network users.
- Work networks are for small office/home office (SOHO) or large workplace networks. Network discovery is turned on.
- Public networks are for networks in public places. Network discovery is turned off, keeping a computer from being visible to other computers. This helps protect the computer from malicious software if it is connected directly to the Internet without going through a router or a mobile broadband connection.
In addition to connecting to one of three types of networks, modern operating systems can also join networks as part of a workgroup or domain. Home networks are usually part of a workgroup, while company networks are normally part of a domain.
Workgroup
Joining a workgroup creates a peer-to-peer network. This means that all computers are peers, and no computer has control over another computer. All accounts are local; therefore, a user must create an account on every computer. Typically, there are no more than 20 computers in a single workgroup. Once logged in to the workgroup, all files can be accessed without any password protection. All computers in a workgroup must be on the same network or subnet.
Domain
Computers that join a domain are part of a client/server network. One or more computers are servers that are used to control the rights and permissions for all devices that are members of the domain. The domain users must provide credentials each time they access the domain. A user with a domain account can log on to any computer on that domain without creating an account on every computer. The number of computers that can belong to a single domain is almost limitless. Computers on different networks or subnets can belong to the same domain.
Network connections provide connectivity between a computer and the Internet, a network, or another computer. The network connection settings specify how a computer will connect to a network. A computer may join through a wired, a dial-up, a wireless, a Virtual Private Network (VPN), or any other type of connection.
Things to consider:
- When using multiple network adapters, rename each connection so each can be easily identified
- Verify the required connection settings for each adapter
- Create dial-up, VPN, or other direct connections by using the new connections wizard
- Specify the order in which protocols and network providers are accessed
- Only install and enable the network protocols that are needed
To manage network connections, click on Network and Internet Connections in the Control Panel of Windows XP or the Network and Sharing Center in the Control Panel of Windows 7. Then click on the Change adapter settings in the left panel. This will open the Network Connections window. Each network connection can be enabled or disabled, repaired, or IP settings can be configured.
Virtual Private Network (VPN)
A Virtual Private Network (VPN) is one of the most secure ways to connect to a private Local Area Network (LAN) from a remote location. The Internet can be used to transport data packets securely using encryption.
VPNs are often used by companies to connect remote offices with their main location so that data and network resources can be shared. Remote workers can also connect to their company’s location using a VPN connection. Authentication is used to allow or deny a user access, and private data is protected by encryption. A VPN creates a secure connection between two points.
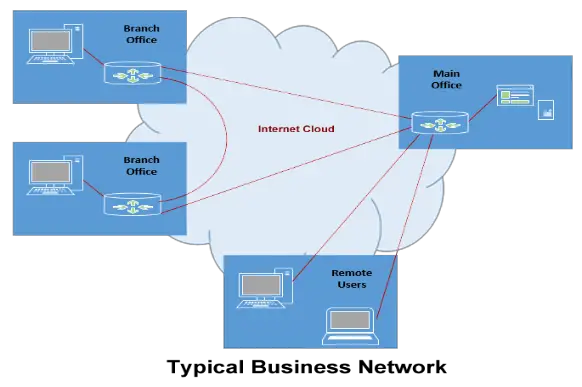
Figure 1: Diagram showing point-to-point and remote VPN Connections
Remote Access/Branch Office
Two new network features added to Windows 7 are:
- DirectAccess provides Internet connectivity to client computers when no VPN is enabled. For more information about this feature, please view the following video – Windows 7 DirectAccess User Experience (11:13).
- BranchCache is used to copy content from a remote file or Web server and cache the contents at branch office locations. This allows data to be accessed at the local branch office instead of having to cross a Wide Area Network (WAN). Details on using BranchCache can be viewed at BranchCache (4:19).

Figure 2: Image of a laptop connecting to a workstation or server using Direct Access
Dial-up Connections
Dial-up connections are created when a modem sends a signal over a telephone line to a modem at a remote location. Dial-ups Settings can be changed from the Connection tab in the Internet applets options.
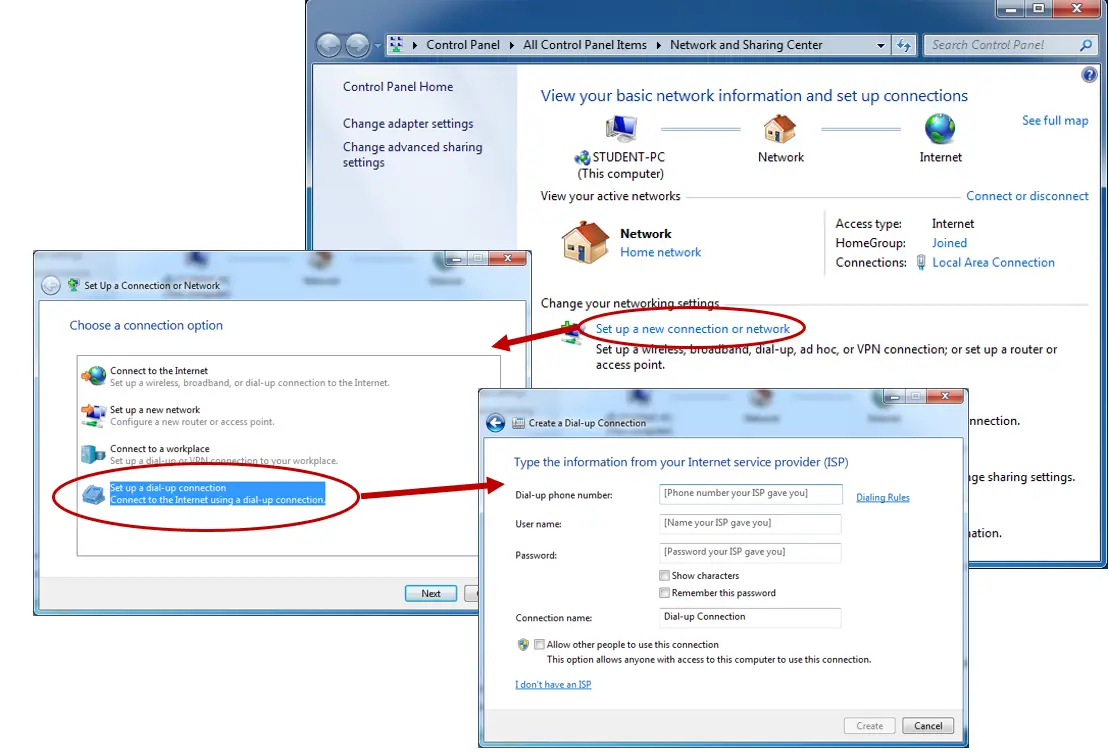
Figure 3: Screens displaying how to configure a computer to make a dial-up connection
Wired Connections
Wired connections are the fastest and most secure network connections. They allow a connection to a LAN and the Internet through a network interface card. This is usually an Ethernet type connection.
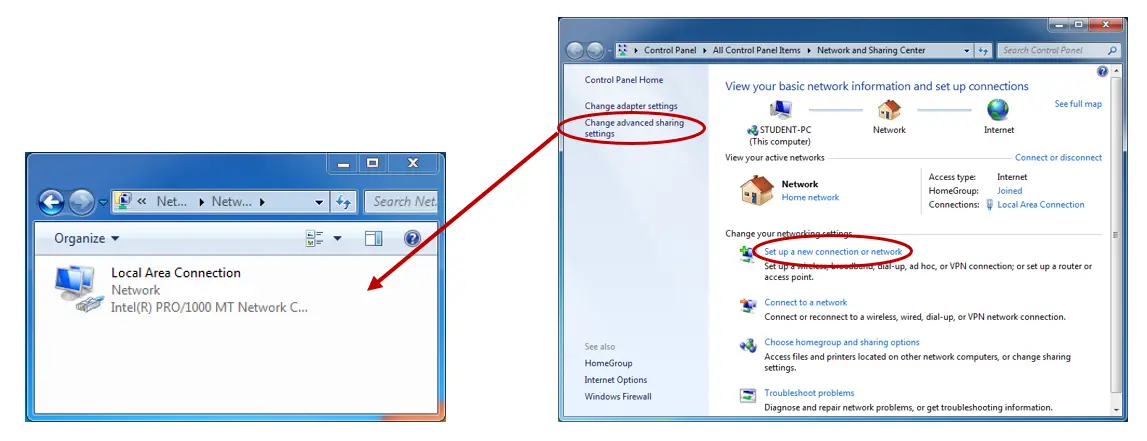
Figure 4: Screens displaying how to set up a Local Area Connection
Wireless Connections
A wireless connection allows a connection to a Wireless Local Area Network (WLAN) to access network resources and the Internet. A connection can be made to a broadcasting or hidden network by manually typing in the required information, such as providing the Service Set Identifier (SSID).
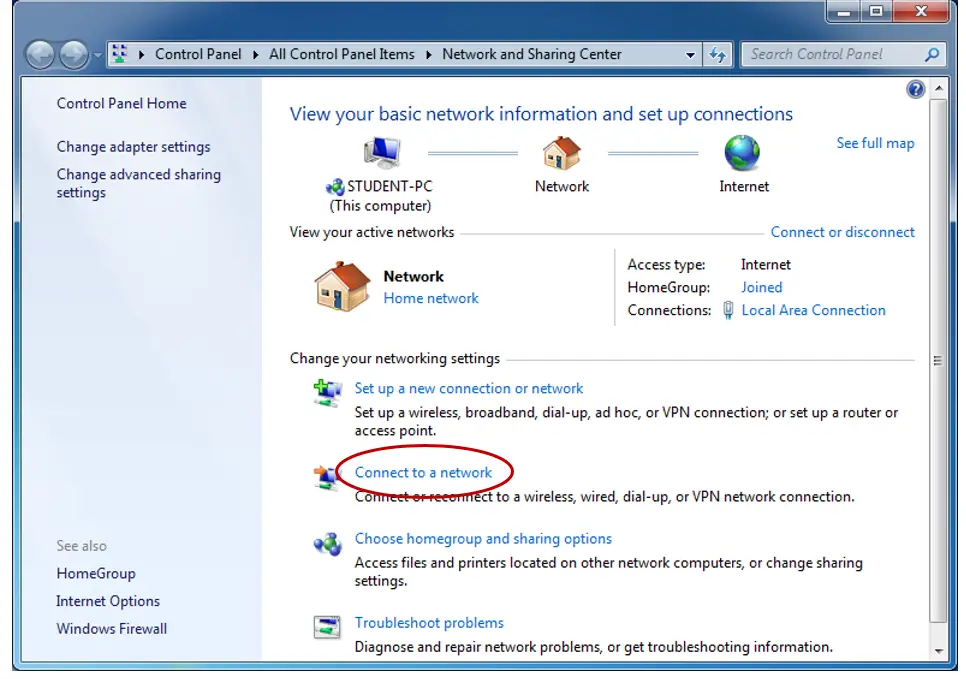
Figure 5: Screens displaying how to set up a Wireless Connection
Network Shares
Now that the computer has been connected to a network, how can it get to resources on that network? Sharing a folder allows other computers and users to access information across a network using one of these two options: through the Universal Naming Convention (UNC) or by creating a mapped drive.
1. By typing the share’s name using the Universal Naming Convention (UNC) into the run command or in the network window – a new connection must be made each time access to the share is needed. A UNC starts with two backslashes followed by the server name, another backslash, and then the name of the shared folder.
\\<server_name>\<share_name>
2. By creating a mapped drive – Select Tools on the Explorer window -> Map network drive… -> select a drive letter and either Browse to the share or type the UNC for the share. This makes the share appear as a local drive on the computer.
Proxy Settings
A proxy server is a computer that acts as a type of filter for requests that are made to other servers, especially those on the Internet. When a computer makes a request, the proxy server first checks to see if the site has been cached or if the request should go out to the Internet. Proxy settings can be accessed from the Connections tab in Internet options. The proxy server’s IP address and the port it uses are required.
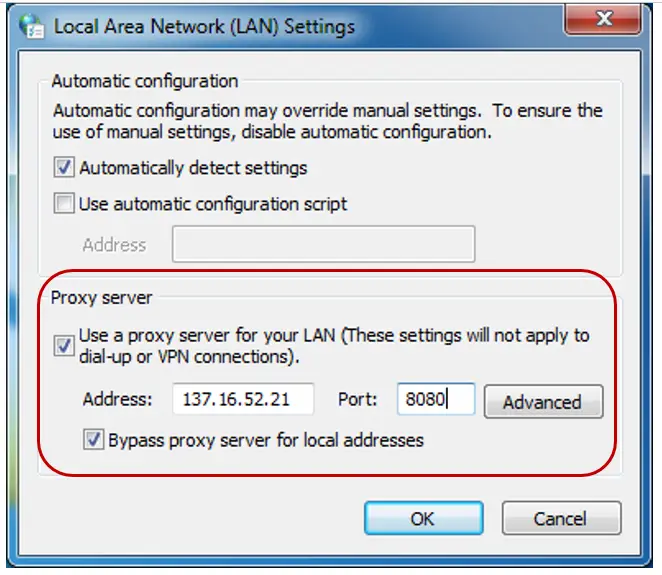
Figure 6: Screens displaying how to configure Proxy Settings
Firewall Settings
A firewall is a must in today’s networks. It can help prevent hackers or malicious software from gaining access to a computer through a local network or the Internet. It can also help stop a computer from sending malicious software to other computers.
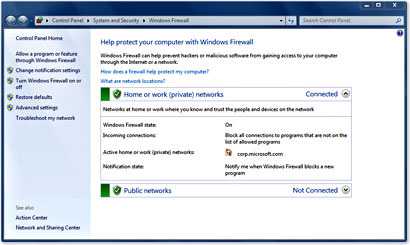
Figure 7: Screens displaying how to configure Firewall Settings
A good firewall blocks everything by default. What is allowed through the firewall can be modified by the user. The program that needs to be allowed can be selected from a list of programs, or if the program is not listed, it can be added to the exceptions list or a specific port can be opened.
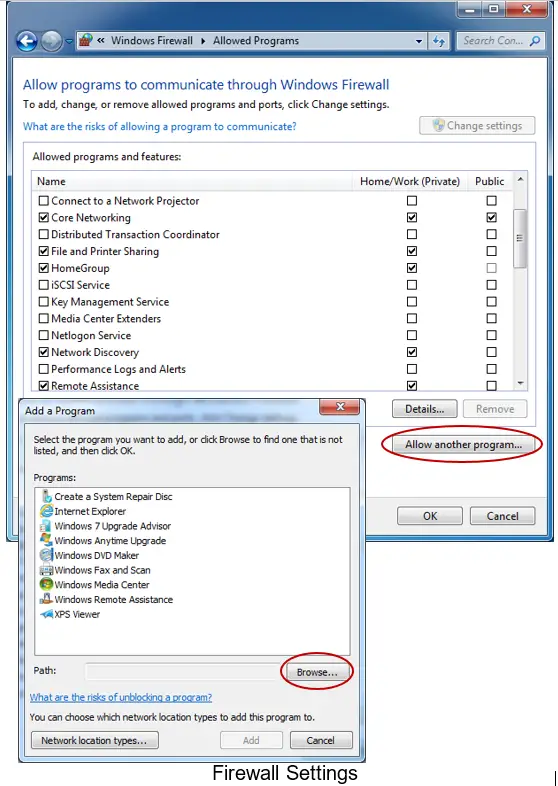
Figure 8: Screens displaying how to configure Firewall Exceptions
To open a port, a user can go to the Windows Firewall applet in the Control Panel, click Advanced settings in the left pane, click Inbound Rules from the left pane, and click New Rule from the right pane, then follow the instructions.
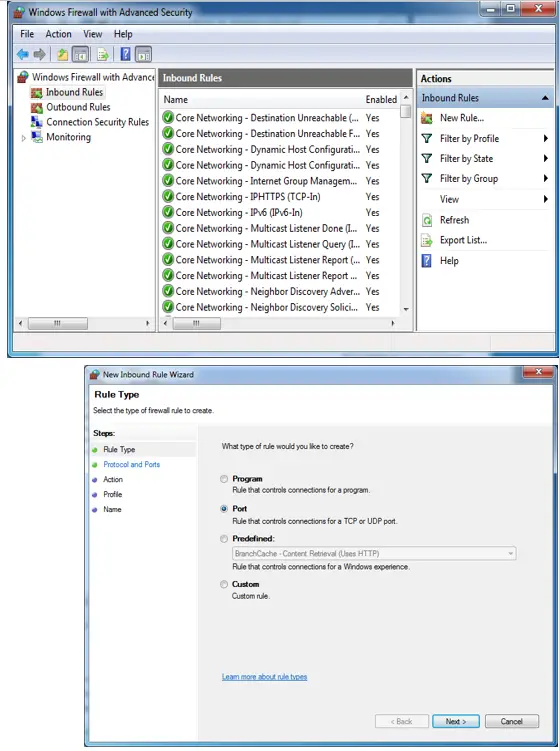
Figure 9: Screens displaying how to configure Firewall Settings
From the left menu of the Windows Firewall applet, a firewall can also be modified for home, work, and public network types.
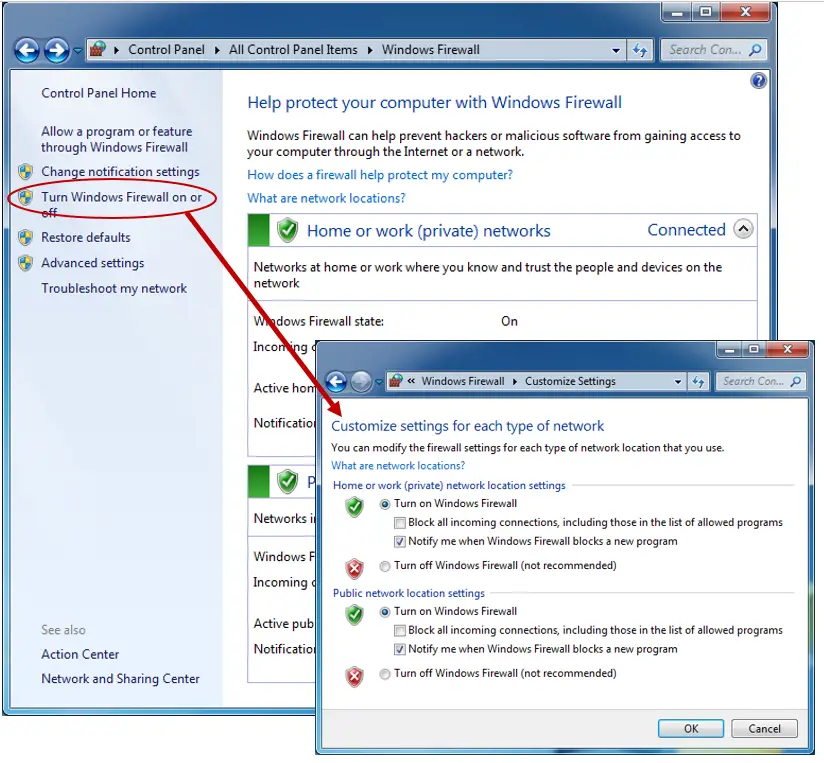
Figure 10: Screens displaying how to make additional configuration changes to Firewall Settings
Summary
In this lesson, you learned important concepts about relating to Windows Networking. Keep the following in mind:
- Common Network Interface Card (NIC) settings, such as logical addressing, and special settings, such as speed and duplex, were explained. How to configure these settings was also described.
- Wireless Wide Area Network (WWAN) standards such as LTE, WiMAX, CDMA were introduced.
- Home vs. Work vs. Public networks are selected to apply the appropriate security settings on a computer connecting to a network.
- All modern operating systems can belong to a workgroup or a domain. The purpose of each was outlined.
- Several types of network connections were discussed. Virtual Private Networks (VPNs) provide private and secure connections to a LAN. A Direct Access connection can be established when no VPN is available. BranchCache is a connection between computers wherein data is cached on Branch Office machines. Dial-up connections are still available. Wired and wireless connections were also described.
- How network shares are created and accessed was outlined.
- Proxy settings can be configured to provide more control over how data on other networks is accessed.
- Configuring a computer’s firewall is very important, especially for home users. Various settings were discussed in this lesson.