There are many ways that computer systems can be infiltrated and infected. Since the 1980s, when computer viruses became increasingly prevalent, companies have spent millions of dollars to protect their systems from malicious intrusions.
Today, malicious software (malware) is readily available for purchase and/or download. This software is often designed with a specific purpose, and often the host computers are unaware that they have been hit with an attack. Some of the more common forms of cyberspace intrusions are detailed next.
Network-Based Attacks
A network intrusion occurs when a computer system is accessed without permission. Such intrusions may go unnoticed depending on the level of firewalls and security associated with the system.
Network-based attacks are attractive because (1) they may often go undetected and (2) the perpetrator(s) are often difficult to trace. Two main forms of network-based attacks are untargeted attacks and targeted attacks.
Untargeted attacks are of concern for the public, as the attack indiscriminately chooses who the attack victims are. If one computer or computer system is heavily protected, the intrusion will just move on to the next vulnerable system.
One example of an untargeted attack includes distributed denial-of-service attacks in which computer systems are hijacked, often without the owners’ knowledge, and used to flood a website (i.e., the website has so many computers attempting to access it that it crashes).
Another popular form of untargeted attacks is phishing. A phishing attack is when a mass e-mail is sent to multiple computers requesting that personal information (banking, Social Security number, etc.) be sent to a specific location. A famous example of this is the Nigerian prince scheme in which victims were solicited to give their banking information or make a small payment in return for a large payment from a Nigerian prince looking to share his wealth. Of course, the victims lost whatever money they paid, resulting in a substantial profit for the perpetrators of this scheme.
Another form of network-based attacks is a targeted attack. Targeted attacks differ from untargeted attacks as they single out a specific business, organization, or user’s system to infiltrate.
Targeted attacks are not random; the victim is deliberately chosen and targeted. The perpetrator may have a personal reason for the attack or could be hired by someone to orchestrate the infiltration. Even more alarming is that the perpetrator could be an insider—someone working for the company being victimized.
Insiders are especially problematic as they do not have to hack into a system because they have legitimate access to it. For example, a disgruntled employee at a power plant would have access to the systems and even the passwords protecting the infrastructure. If this individual shared the information with someone with malicious intent, the damage could be catastrophic.
Wireless Attacks
There are great benefits to wireless services, such as ease of access, the ability to be more flexible, and increased productivity. However, with these benefits also come added security risks.
Wireless networks are often less secure than traditional online networks. Businesses often advertise free Wi-Fi as a way to draw in customers. These open-access networks are easy for hackers to access. Some of the vulnerabilities and attack methods associated with wireless attacks as discussed by Morgan are detailed below:
- Human Error: Individuals who do not have a clear understanding of inner workings of the system can make errors in setup leading to vulnerabilities in the system.
- Rogue Access Points: Rogue access points are created in two ways: (1) the individual who installed the wireless network does so within the confines of another network—that is, a rogue access point (backdoor) into the original system may be created; or (2) hackers with malicious intent can also plant an access point to allow access via that backdoor at a later time. Backdoor access can be as simple as programming a special password that would allow the hacker into the system without the owner’s knowledge.
- Noisy Neighbors: As wireless signals are sent via radio waves, they can experience interference with other sources also using radio waves (e.g., baby monitors, cordless phones, other routers). This can have an effect on the speed or even the accessibility of the network. Noisy neighbor incidents can be accidental, but they can also be orchestrated maliciously by an individual using other wireless devices to deliberately interfere with the network.
- Man in the Middle: In this form of attack, the malicious party intercepts a message; he or she can gather information, alter the message, attach a virus, etc., and then send the message on to the intended recipient. The intended recipient would have no idea that the message has been intercepted by a third party (see Figure1).
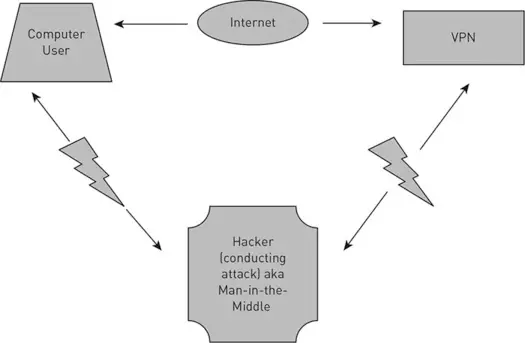
Figure 1 Man-in-the-Middle Wireless Attack Diagram
Man-in-the-Middle Attacks
Man-in-the-Middle attacks are increasing in popularity, and there are six main techniques used by fraudsters to hack into an Internet connection and manipulate or steal data:
- Wi-Fi Eavesdropping: The fraudster hijacks the Wi-Fi connection and intercepts the communication. Public Wi-Fi connections are especially vulnerable. There are several ways in which criminals can hijack a Wi-Fi connection. They can create a fake Wi-Fi node, which tricks individuals into connecting to that node. The fraudster can also intercept the communication of Internet users by hacking an unencrypted connection or hacking the Wi-Fi password. To protect users, passwords should be secure and public networks shouldn’t be used for checking bank accounts, e-mail, and other sensitive information.
- Man in the Browser: This is also referred to as a banking Trojan. The Trojan operates in the background of the computer by modifying banking transactions. The customer may see the correct amount to be transferred on the screen but the browser display is incorrect. The display shows what the customer intended to do, but in reality, the Trojan has manipulated the transaction. For instance, the customer intended to pay 1,000 dollars toward credit card debt. The Trojan instead sent all the money in the account of the customer to a different account held by the fraudster. The screen will show the correct intended transfer of 1,000 dollars and the correct amount of money in the accounts, but when the customer goes to the bank to get money, the bank account will be empty. Even a printed PDF from the online banking site may show that everything is correct, but it’s an illusion. The screen is not always correct. A Trojan can manipulate the screen and make it look like everything is fine when in reality all the money has been stolen.
- Man in the Mobile: Criminals increasingly hack into mobile devices and monitor user activity, such as text messages and apps, to obtain passwords and account authorization information. For instance, if the user texts passwords or the last four digits of the Social Security number, the criminal could then use the information to access banking accounts or other financial information.
- Man in the App: Almost anything can be done via apps, including depositing checks, buying and selling stock, arming the house alarm, preheating the car, and so on. Unfortunately, anybody can develop apps and put them in the app store. This, of course, includes criminals who develop apps with built-in malware such as Trojan horses. In addition, many apps are not secure from hacking, and fraudsters are diligent to abuse any such security flaws. For instance, many people use mobile apps for online banking. If the customer installed an app with a Trojan, the criminal could then access all information typed in by the customer and the bank account.
- Man in the Cloud: File-sharing tools such as Google Drive, DropBox, and Microsoft OneDrive have become popular among businesses and academics for collaborative work. They are also popular among individuals who are sharing files, such as music. Clouds have vulnerabilities related to session management that are easily exploited by hackers. For instance, DropBox and other services don’t require signing in every time a user accesses the account. Also, synchronization of the files is often automatic without a sign-in requirement. This makes it very easy for criminals to access shared files. If these files contain confidential or sensitive information, it can have devastating consequences. Or imagine the files have information about a pending patent or technical specifications only known to the company. This information would be accessible, and criminals could sell it to companies who may reverse-engineer a product. Industrial espionage is rampant, and cloud-based services create substantial risks for companies.
- Man in the Internet of Things: Our connected devices, such as alarm systems, cars, thermostats, appliances, and TVs, have basic operating systems that can be hacked and manipulated by fraudsters. Hackers can take over the steering of a connected car, airplane, or ship, turn off your house alarm, and change how your appliances work. The assumption that these devices don’t need sophisticated cybersecurity measures is not only false—it’s dangerous. Imagine someone taking over the control of a car and driving it over a bridge. That could be the future of assassinations. The hacker could be in a different country, hired and paid to kill a person via a car accident. As your daily life, including your home, becomes more connected to the web, and therefore more connected to potential criminals, this problem will grow.