The article provides an overview of computer virus, including their definition, types, and how they spread. It also outlines the associated risks to both computers and mobile devices, emphasizing the threats posed by traditional viruses and advanced persistent threats (APTs).
A virus is a “small software program designed to spread from one computer to another and to interfere with computer operation.” A virus is a code that will duplicate itself into a host program when it is activated.
Every company has at least one employee who will click on anything and open any file he or she receives. Not surprisingly, hackers are well aware of that, and so 90% of all cyber intrusions start with a phishing e-mail.
Virus files are typically executable files—that is, a file that the computer directly executes. They typically end in .exe. This may be a hidden extension, however, to prevent users from becoming suspicious. Users cannot read executable files. Once the user opens or runs the program, the virus spreads further and infects other programs or the entire computer.
Imagine you downloaded a music file from the Internet that was infected with a virus aiming to disable your Excel files. When you run your Excel program, the virus is activated and starts to destroy your Excel files.
Image 3.1 Computer Virus
There are three main types of viruses: (1) shell viruses, (2) add-on viruses, and (3) intrusive viruses.
Shell viruses form a shell around the original code and the original host program with the purpose to take over the functions of the host program.
Add-on viruses attach to the original code, changing the startup information of the program. The viral code then executes before the original code, interfering with the program that the user attempts to run.
Intrusive viruses overwrite the original code, which can make the host program dysfunctional.
Viruses are now able to operate in stealth to avoid detection. This is called an advanced persistent threat (APT). APTs are “cyber-attacks executed by sophisticated and well-resourced adversaries targeting specific information in high-profile companies and governments, usually in a long term campaign involving different steps.”
Originally, APT only referred to cyber intrusions against military units, but APTs are now targeting a wide range of industries and governments. APTs can be distinguished from traditional threats by their characteristics. Table 1 shows the differences between traditional attacks and APT attacks.
Table 1 Traditional Attacks versus APT Attacks
|
Traditional Attacks |
APT Attacks |
|
|
Attacker |
Single hackers or a loose community of hackers | Highly targeted attacks with a clear objective |
|
Target |
Typically individual computers or devices, nonspecific | Skilled and highly organized and resourced hackers |
|
Purpose |
Profit, fame, challenge | A long-term campaign with persistent attacks |
| Approach | Single run, mostly easy to detect |
Stealthy and evasive attack techniques that can stay undetected |
Both traditional and APT attacks pose five main risks for private computer users, companies, and government entities: (1) disable computers and mobile devices, (2) send spam, (3) provide access to computers, (4) steal personal information, and (5) hijack the user’s web browser.
Image 3.2 Credit Card Theft

Risks Created by Viruses
1. Disable computers and mobile devices
Some viruses can cause a computer or mobile device to stop functioning properly. Disabling devices carries great risks for companies and people. These devices may disable alarm systems in people’s homes or businesses, or they can disable the defense network of the government and the military. One such incident occurred in 2008 when a virus disabled the defense network of the Department of Defense (DoD). The virus was transferred to a DoD computer via an infected USB flash drive brought in from the outside by an authorized user. The virus invaded classified and unclassified networks and gave control of the computer system to the author of the virus. It took 14 months and $1 billion to recover from the attack, and the true extent of the compromise remains unknown.
2. Send spam
Viruses are often capable of accessing the address book of the infected computer or mobile device and sending spam messages with itself attached to friends, family, and colleagues of the victim. If these users opened the attachment in the belief it came from a friend, they infected their own computer or mobile device. This is also a common scheme through Facebook. Users may receive an e-mail from a “friend” with a picture or video attached and are asked to open the file. The file contains a virus, and the e-mail did not come from their Facebook friend.
3. Provide access to computers
Viruses may be written with the purpose to give the malicious writer control over the computer or mobile device. Control over the device can serve the purpose of stealing data, controlling certain functions of the computer, or manipulating files on the computer, such as encrypting files or changing the security settings. If an outside person changes the security setting, the owner of the device may be locked out. Imagine a hospital being locked out of their computer system. Without access to medical records, patients cannot receive treatment.
4. Steal personal information
Criminals often target computers to gain information they can use to steal someone’s identity, steal his or her money, or get information from the computer that would help them make money. For instance, a criminal may try to get information about stocks before the market opens to make certain bids that will be financially beneficial. This type of trading is illegal, of course.
5. Hijack the user’s web browser
Viruses can also hijack a computer’s web browser. By default, the devices download messages without users having to open the message and initiating the download. Users can prevent this problem by disabling automatic downloads of text messages and e-mails. The person controlling the computer or mobile device can push automatic messages to the victim or users found in the device’s address book.
Risks to Mobile Devices
As discussed above, the risks created by viruses are not only risks to computers or networks but also to other electronic devices, such as smartphones, drones, home security cameras, baby monitors, and other devices that use Bluetooth or are connected to the Internet.
Smartphones and Bluetooth devices, such as health trackers like Fitbit, have been swarming the market, and many users are constantly connected to the Internet. This technology has also become a popular target of cybercriminals who understand the opportunities to exploit device vulnerabilities.
Smart devices have several vulnerabilities, including web browsing, Wi-Fi, multimedia message service (MMS), short message service (SMS), Bluetooth, applications, and e-mails. Malicious code writers have developed viruses that target mobile devices. These viruses are generally referred to as MMS viruses. Similar to computer viruses, these MMS viruses can disrupt phone service, steal information, block data, track the user’s movement, force text messages to friends and others in the address book, etc.
Users may never find out that their mobile devices are infected and unwittingly spread the virus to other devices, including computers via USB or Bluetooth connection.
Some researchers have warned that devices such as Fitbits could contain a virus, and if the user connects it to a company computer to charge it via USB cable, the virus could spread into the computer network of the company. Although this is currently a hypothetical scenario, it certainly presents a serious danger.
Another threat that MMS viruses pose is their ability to randomly scan the phone network and contact mobile phone users who are not in the address book. MMS viruses can infect large numbers of smartphones.
See Table 2 for examples of types of viruses.
Image 3.3 Computer Locked
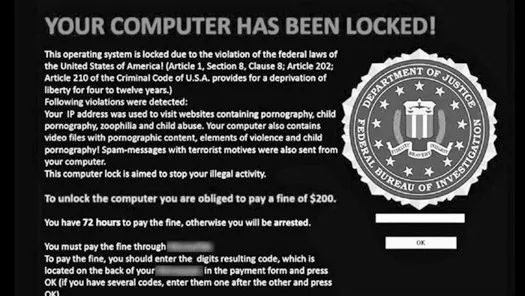
Table 2 Types of Viruses
| Type | Example | How it works |
| File Infector Virus |
Jerusalem Cascade |
Infect program files, such as .com or .exe |
| Boot Sector Virus | Disk Killer
Michelangelo |
Infect the system area of the disk—the boot record. |
| Master Boot Sector Virus | NYB
Unashamed |
Infect the system area of the disk—the boot record.
But the location of the viral code is different. Typically saves a legitimate copy of the master book sector in a different location. |
|
Multi-partile Virus |
Anthrax
Tequila |
Infect boot records and program files. |
| Macro Virus | Melissa
Nice Day |
Infect data files. |
Computer Virus Key Takeaways
Understanding the nature, types, and consequences of computer viruses is crucial in today’s interconnected digital world. These threats not only compromise individual devices but can also disrupt entire organizational and governmental infrastructures. From corrupting essential data and disabling devices to hijacking systems and stealing sensitive information, viruses pose a wide range of risks. Advanced threats like APTs add another layer of danger, utilizing stealthy, long-term attacks against high-value targets. Recognizing these risks is essential for developing robust cybersecurity strategies and defense mechanisms. In practical terms, this knowledge supports the design of secure software, informed user behavior, and stronger protection for networks and devices—making it a vital foundation for IT professionals, businesses, and everyday users alike.