The article provides an overview of cybersecurity threats originating from local, national, and international sources, detailing various actors and motivations behind these threats. It broadly covers insider threats, activist and politically motivated national attacks, and sophisticated international cyber espionage, hacking, and terrorism targeting critical infrastructures and organizations.
Threats to cybersecurity originate from three sources: (1) local threats, (2) national threats, and (3) international threats. According to the Department of Homeland Security (DHS), a cyberthreat “refers to persons who attempt unauthorized access to a control system device and/or network using a data communications pathway.”
Cyber threats originate mainly from hacktivists, hackers, foreign governments, military units, terrorists, industrial spies, and organized crime groups.
Local Threats
Local threats are threats that originate from inside the company or organization. These insider threats are very difficult to combat.
Insider threats are defined as “harmful acts that trusted insiders might carry out; for example, something that causes harm to the organization, or an unauthorized act that benefits the individual.”
An insider threat manifests itself as “human behavior that departs from compliance with established policies, regardless of whether it results from malice or disregard for security policies.”
Insiders are people who are current or former employees of a company. These current and former employees have much knowledge about how the company operates, the computer systems, vulnerabilities, and accessibility.
Insiders can also be people who have in other ways, possibly as contractors, obtained information about the company that enables them to break into the computer system. They often either know login information and passwords or have friends inside the company who may provide them with access to the computer systems.
According to national surveys, these insiders are the second-greatest threat to a company’s cybersecurity, only trumped by hackers.
Some of the most common insider cybersecurity crimes are accessing and/or stealing sensitive information, fraud, violation of copyright laws, and negligent use of classified information.
The most serious insider cyber crimes include cyberespionage, sabotage, terrorism, embezzlement, extortion, bribery, and corruption.
Most companies are ill-prepared for insider threats because they are mainly concerned about attacks into their computer system from the outside and therefore protect only their network border.
Companies also believe that it takes substantial computer skills to steal or expose information, or delete or alter data. This is not necessarily true when all it usually takes to get into a data bank is a password. Employees often trust each other and may share passwords and other information that should not be shared.
Companies also often give all employees unrestricted and unnecessary access to information. Even employees with low skills can easily steal, leak, or sell information that is highly sensitive.
Types of Insider Threats
There are three main types of insider threats: (1) malicious insiders, (2) exploited insiders, and (3) careless insiders.
Malicious insiders are the least common but the most costly because they strategically cause data breaches, often with the goal to cause great damages.
Exploited insiders are people who are “tricked” by others into giving up access information or into accessing the information themselves and giving the information to an external party.
Careless insiders may delete or expose sensitive information by accident, by either pressing a wrong key or other mistakes.
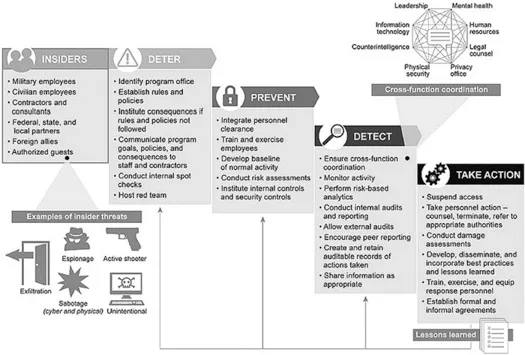
Figure 5.1 Insider Threat
National Threats
National threats originate from individuals inside the United States aiming to attack local or national governments and infrastructures. These individuals are often displeased with the government and/or specific causes (i.e., anti-abortion activism, animal rights activism, environmental activism).
Displeasure with the Government
Individuals who are displeased with the government may work independently or join together to form an organization. They typically launch cyber attacks in opposition to certain initiatives, bills, or laws. These groups are comprised of individuals from different countries with a loose and decentralized demand structure.
They operate mainly on ideas, and attacks may be planned and carried out by a few members. They operate in secrecy and have great media awareness. These groups are often motivated by the defense of freedom, free speech, privacy, individuality, and meritocracy.
Image 5.1 Anonymous
One of the most well-known hacker groups is “Anonymous,” a global hacker community. As a protest to the Canadian anti-terror bill, Anonymous launched a denial-of-service-attack on the web servers of the Canadian federal government. Anonymous flooded the website with requests, which resulted in a shutdown of the website.
Specific Causes
There are numerous groups who launch cyber attacks trying to accomplish specific causes. These groups include the White supremacists, left environmentalists, animal liberation groups, and anti-abortion groups.
These groups can pose significant threats to critical infrastructures. For instance, the Earth Liberation Front has long opposed nuclear power plants and has been a continuing threat. If they were able to hack into a power plant control system and remotely operate the system, the consequences could be devastating.
Another threat is attacks against Internet service providers (ISPs). In 1996, a hacker, allegedly a member of the White supremacists, disabled a Massachusetts ISP and destroyed parts of their record-keeping system. He signed with the threat “you have yet to see true electronic terrorism. This is a promise.”
International Threats
International threats originate in individuals outside the United States. International threats take three main forms: (1) nation-states hacking or spying on trade and other secret information, (2) advanced hackers aiming at large corporations, and (3) terrorists looking to identify and exploit vulnerabilities in our infrastructures and to infiltrate military and government systems.
1. Nation-states hacking or spying on trade and other secret information
Nation-states pose a significant threat to the United States as they are educated and well-funded operatives with very specific targets and strategies. These states do not need to have the most sophisticated technology, especially if they are capable of launching a large number of attacks in a short period of time.
These states may use brute-force attacks because they are inexpensive and relatively easy to carry out. One of the most persistent threats originated in China. China’s military cyber unit 61398 has been credited with hacking attacks on hundreds of companies across more than 20 industries that have strategic value for China. According to the DHS, the Chinese military attacked 23 natural gas pipeline operators over a 6-month period, from December 2011 until June 2012. The Chinese cyberspies stole information that could sabotage U.S. gas pipelines by controlling and altering the operation of the pipelines.
2. Advanced hackers aiming at a large corporation
Advanced hackers are typically motivated by financial or political goals. Hackers who target financial institutions have turned increasingly to corporate espionage aiming to steal data that can be sold to third parties or used for insider trading.
Financially motivated hackers may also engage in identity theft and money laundering. For instance, in 2015 nine men were arrested by the FBI for stealing sensitive data from the New York Stock Exchange for financial gain. Over a time frame of 5 years, dozens of rogue stock traders sent requests to hackers, working from Ukraine, asking for specific news releases that were to be published. The stock traders used the information from the news releases for illegal insider trading purposes, that is, to buy and sell stock for illegal profits. Overall, the illegal profits totaled over $100 million for traders and hackers.
3. Terrorist Threats to Infrastructures and Military and Government Systems
Cyberterrorism;
-
- involves using computer networks and technologies as a means for conducting attacks, and targets critical national infrastructures or governmental assets, has a psychological, social, political or religious motive, causes harm to individuals or groups, or physically damages infrastructures or assets.
Cyberterrorism attacks typically target the government or critical infrastructures, and they often take the form of denial-of-service attacks, cyber espionage, and cyber warfare. Since the first cyber attacks in the early 90s, cyber terrorists have become much more sophisticated in their attacks. For instance, in 1997, communication of the U.S. Federal Aviation Administration with their control tower was shut down for 6 hours by a hacker from Massachusetts. In 2006, the Bureau of Industry and Security at the U.S. Commerce Department had to disconnect their computers from the Internet due to a cyber attack. The cyber attack successfully disabled employees to do their work.
Cyberterrorism attacks on national infrastructures are an even greater threat. There is an abundance of targets, which, if attacked, could cause substantial damages to the U.S. population and economy. Especially vulnerable infrastructures are energy systems, emergency services, telecommunications, banking and finance, transportation, and water systems.
In 2004, cyber terrorists attacked police emergency services, which resulted in fake calls and deployment of police to fake locations. In the case of a double attack, a cyber- and physical terrorist attack, police may not be able to respond quickly if they are deployed elsewhere.
The Department of Defense is well aware of the threat posed by attacks against critical infrastructures, but more than 90% of networks and infrastructures are operated by the private sector and vulnerabilities are often not addressed comprehensively due to time constraints, costs, or lack of understanding of the risk.
Cybersecurity Threats Key Takeaways
Understanding the various cybersecurity threats—whether local, national, or international—is essential because these risks directly affect the security and stability of organizations, governments, and critical infrastructures. Cybersecurity measures must address insider threats by strengthening internal controls and limiting access to prevent data breaches and sabotage. National and activist-driven threats demonstrate how cybersecurity is vital to protecting public services and infrastructure from politically motivated attacks. Furthermore, international cybersecurity challenges, including espionage by nation-states and cyberterrorism, highlight the need for robust global defense strategies. By recognizing and addressing these diverse cybersecurity threats, organizations and governments can better safeguard sensitive information, maintain operational continuity, and protect national security in an increasingly digital world.