The article provides an overview of encryption, explaining its purpose in securing data and how it functions through concepts like public and private keys. It also outlines core components of proper encryption, potential cyber threats, and practical steps users can take to encrypt their computers.
Encryption is the obfuscation that is fast when you know the secret but very slow when you don’t. Encryption of data is still the most effective way to protect it from being stolen. It is also called cryptography. Even though the NSA has the capability to crack encrypted data, it is very difficult and resources intense. Also, some suggest that even the NSA cannot decrypt data encrypted with an Advanced Encryption Standard.
Proper encryption encompasses five components: (1) attribution, (2) integrity of data, (3) nonrepudiation, (4) infinity, and (5) scrambled text.
Attribution refers to a digital signature providing proof of authorship. The signature may be used to provide legal proof of a person’s communications and activities. It is imperative that only the person who has authority to sign can actually do so. If someone could posture as the signatory, the system is not secure.
Imagine that the DoD receives a request for data about their latest stealth fighter plane from the president of the United States. In actuality, the request for information comes from a Chinese hacker working for the Chinese government with the intent to steal the data and reverse engineer the fighter jet. This type of cyberespionage is very common and can become a threat to national security.
The integrity of data “refers to protecting information from being modified by unauthorized parties.” The only information that is correct also has value. In addition, if data is manipulated, this can prove very costly.
Imagine that the CIA sends information to the president of the United States about a possible nuclear attack against the United States by North Korea. In reality, the information was manipulated and there is no nuclear threat. The president could potentially authorize a preemptive strike against North Korea, which could lead to a war.
Nonrepudiation, also called availability, means that persons authorized to access information always have access to the information. One of the main cyber attacks today includes the denial of information for authorized persons. There are two main ways to deny access: denial-of-service (DoS) attacks and distributed denial-of-service (DDoS) attacks.
In a DoS attack, the attacker may flood the network and overload it, which then makes it impossible for the authorized user to access the network and information.
In a DDoS attack, the attacker typically accesses an innocent person’s computer to attack other computers by overwhelming them with data requests. In that sense, the attacker distributes the data from one or several computers that the attacker took control of prior to the attack by exploiting a security vulnerability of the computer.
One of the largest DDoS attacks of its kind, if not the largest, was called the Mirai botnet. The Mirai botnet brought down much of the Internet in the United States and Europe, including Twitter, Netflix, Reddit, and CNN, in October 2016.
The Mirai botnet was distinct from other attacks because it took advantage of the vulnerabilities of the Internet of Things (IoT). The IoT includes iPads, health trackers, smartwatches, and other consumer goods connected to the Internet.
The sheer amount of IoT devices that have flooded the computer market has greatly increased the access of hackers to personal information and the ability of hackers to hijack the devices to carry out a DoS attack. These goods often have much less security than computers and are therefore easy to access by a hacker, making the attack much larger.
Infinity means that there should be such a great number of combinations to guess the encryption key that it would take around 1.5 million (18 zeros) years. This number would practically be infinity.
The final condition is that the text must be scrambled by using a mathematical algorithm. The scrambled text is also referred to as ciphertext.
“Keys” are used to encrypt and decrypt the text. To encrypt the text, a public key is used. This key is known to everyone and is distributed to the public. Since this public key can only encrypt the text (scramble the text) but not decrypt, it does not need to be kept secret.
A private key, however, must be kept private because it decrypts the text—that is, it makes it readable. The private key should only be known to the person receiving the message. If other people obtained the private key, they could read the text that was meant to stay private. For instance, messages sent by military leaders to their troops need to be kept secret or the safety of the troops could be in danger. If the enemy knows how the Navy SEALs are going to free a person, they could get killed during their mission.
Figure 1 and 2 illustrate how encryption and decryption work.
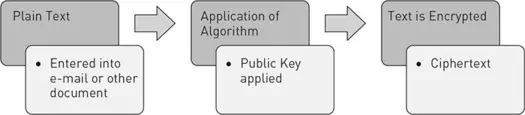
Figure 1 Encryption
The process of decryption is basically the reverse:
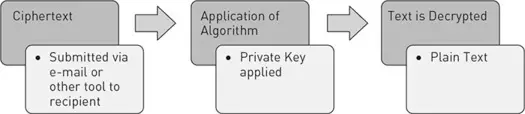
Figure 2 Decryption
Encryption & Data Loss
Users can sometimes lose encrypted data from hard drives, flash drives, or SD cards. This could happen when a user forgets the password, deletes the files, or ransomware encrypts data making it inaccessible. When any of these situations occur, the user can recover data from the backup or use the Windows Restore feature. However, recovering encrypted data can be complex and often require professional data recovery services.
What Can You Do?: Encrypting Your Computer
macOS
If you own a Macintosh computer, you can easily encrypt your data.
-
- – Open System Preferences
- – Click on Security and Privacy
- – Click on FileVault
- – Turn on the File Vault
- – You will receive a recovery key (DO NOT LOSE IT)
- – To turn the Encryption off, you will need the key
PC
If you own a PC and you have Windows 10 Professional, you can use the software BitLocker, which is already built in.
-
- – Control Panel
- – System and Security
- – BitLocker Drive Encryption
If you own a PC and you don’t have Windows 10 Professional, you can use the software VeraCrypt.
-
- – Download VeraCrypt
- – Follow the instructions on the screen
Encryption Key Takeaways
Understanding and implementing encryption is critical in today’s digital landscape where sensitive information is constantly at risk. From safeguarding personal data to protecting national security assets, encryption ensures that only authorized parties can access and interpret confidential information. Its core components—such as attribution, integrity, nonrepudiation, infinity, and data scrambling—work together to create a robust defense against cyber threats like data tampering, identity spoofing, and denial-of-service attacks. Encryption also plays a vital role in securing communications across governments, military operations, and private enterprises. With the rise of cyberespionage and IoT vulnerabilities, applying encryption practices such as FileVault on macOS or BitLocker and VeraCrypt on Windows systems is more important than ever.