The article provides an overview of various types of network and wireless attacks, including denial-of-service, spoofing, sniffing, and man-in-the-middle techniques. It also discusses how these attacks exploit vulnerabilities in protocols and systems, and outlines basic prevention methods and security tools used for network protection.
Introduction
In this lesson, you will learn about the various threats that an attacker can launch against a network. Attacks on a specific protocol or service are attempts to take advantage of a specific feature or to use the protocol or service in a way that was not intended. You will gain an understanding of different types of network attacks, and how to use assessment tools to help determine security.
Lesson Objectives
By the end of this lesson, you will be able to:
1. Analyze and differentiate among types of network attacks.
2. Analyze and differentiate among types of wireless attacks.
Instruction
Denial-of-Service Attack
The goal of a denial-of-service, or DoS, attack is to deny access to authorized users making the network unavailable (remember the three underlying security principles, confidentiality, integrity, and availability). A distributed denial-of-service attacks uses many zombies, or soldier attackers to overwhelm a target.
To prevent DoS and DDoS attacks, ensure patches and upgrades are current, change time-out period for TCP connections, distribute the workload across server systems, and block external ICMP packets at the border. Recall that command-line commands such as ping use ICMP packets.
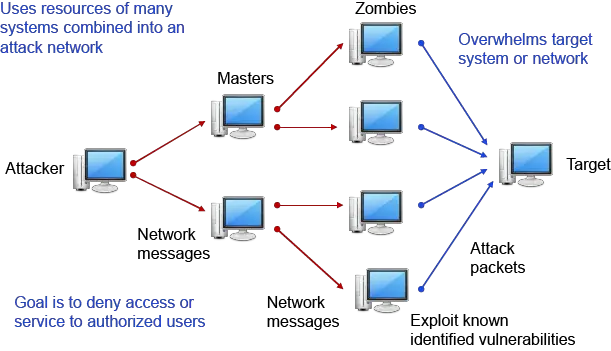
Figure 1 Denial of Service Attack: Graphic illustrates denial of service attack as described in the section above.
Three-Way Handshake
You should have a basic understanding of the three-way handshake that the TCP/IP protocol uses to establish a connection.
- First, System 1 sends a SYN packet to System 2 indicating a desire to communicate with the system.
- Then System 2 responds to System 1 by sending back the SYN packet combined with an ACK packet to indicate its willingness to accept communications.
- Once System 1 receives the SYN/ACK packet, it responds with an ACK packet and communications are then established between the systems.
Please see Figure 2.
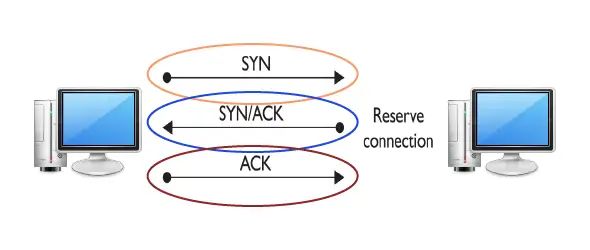
Figure 2 Graphic illustration of a three-way handshake process as described above.
SYN Flood Attack
A SYN flood attack takes advantage of the three-way handshake by overwhelming the target with SYN requests to a bogus server. If the attack can outpace the requests’ timing-out, the target will be in limbo waiting for system responses that do not exist. For instance:
1. Communication request sent to target system using a faked IP address
*If the attacks outpace the requests timing-out, then systems resources will be exhausted.
2. Target responds to faked IP address
3. Target waits for non-existent system response
4. Request eventually times out
See Figure 3 for an example.
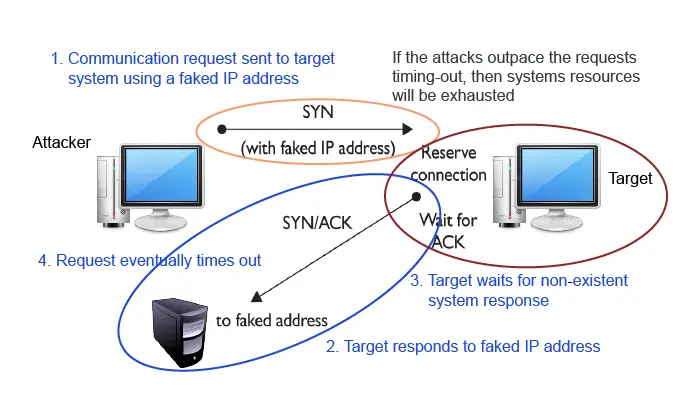
Figure 3 SYN Flood Attack using a three-way handshake.
Ping of Death (POD)
A Ping of Death attack is an example of a DoS attack which targets a specific protocol or operating system. The attacker sends an Internet Control Message Protocol (ICMP) ping packet equal to or greater than 64KB. This type of packet should not occur naturally. Some systems cannot handle the packet and will hang or crash.
Trapdoors and Backdoors
Originally, backdoors referred to efforts by software developers to ensure access to a program that bypassed the normal access methods. Overtime, this practice has come to be known as creating a trapdoor into a program.
One problem with a trapdoor is that since it is hard-coded into the program, it can be very difficult, if not impossible, to remove. A benefit to software developers and system administrators in using a trapdoor is that it ensures access to a program even if the normal access methods fail. However, this benefit is now a vulnerability. The trapdoor offers full access into the system where an attacker could cause serious harm.
More recently, a backdoor has come to refer to the programs or code introduced by an attacker that has compromised a system. A few common backdoor programs are Netbus and Back Orifice which both allow remote access to unauthorized system users.
The purpose of the backdoor is to grant the attacker future access to the system even if the original vulnerability used to attack the system has been fixed.
Usually, backdoors are installed on systems by unauthorized users or attackers. However, they can also be installed by authorized users who inadvertently run a Trojan horse program on their machine which then installs the backdoor.
Similar to the backdoor, another method employed by attackers is to install a rootkit on a system that ensures continued root access for the attacker.
Null Sessions
A null session is a connection to a Windows inter-process communication share (IPC$). A vulnerability exists in Microsoft Windows systems prior to the XP and Server 2003 versions of the operating system. The Server Message Block system (SMB) allows users to establish a null session. A wide range of tools and malware use this vulnerability to achieve their aim.
One way to defend against the creation of null sessions is to upgrade the systems to Windows XP, Server 2003, or newer version. You can also limit TCP ports 139 and 445 to only allow trusted user access.
Sniffing
Sniffing occurs when an attacker examines all network traffic as it passes their NIC independent of whether or not the traffic is addressed to them or not.
Network sniffing can be accomplished with a software application, hardware device, or a combination of the two. Sniffing can be used to view all network traffic or it can target a specific protocol, service, or even string of characters such as a login or password.
Some network sniffers are designed not just to observe all traffic but to modify some or all of the traffic as well. Network administrators may also use sniffers to analyze network traffic, identify bandwidth issues, and troubleshoot other network issues. Physical security is important in preventing the introduction of sniffers on the internal network.
IP Address Spoofing
In a specific DoS attack known as a smurf attack, the attacker sends a spoofed packet to the broadcast address for a network, which distributes the packet to all systems on that network.
In the smurf attack, the packet sent by the attacker to the broadcast address is an echo request with the From address forged so that it appears that another system (the target system) has made the echo request.
The normal response of a system to an echo request is an echo reply, and it is used in the ping utility to let a user know whether a remote system is reachable and is responding. Should the attacker send several of these spoofed requests, or send them to several different networks, the target can quickly become overwhelmed with the volume of echo replies it receives.
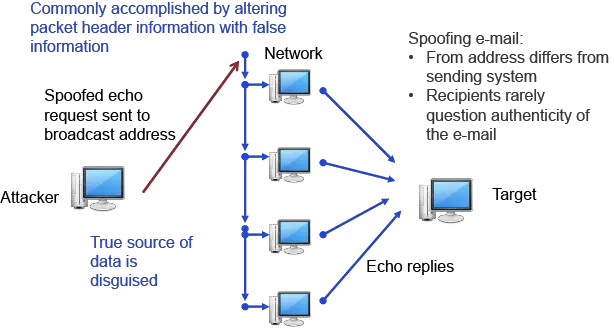
Figure 4 ID Address Spoofing: Graphic illustrates how an attacker is pretending to be a legitimate originating source.
Spoofing and Trusted Relationships
Spoofing can also take advantage of a trusted relationship between two systems.
If two systems are configured to accept the authentication accomplished by each other, an individual logged onto one system might not be forced to go through an authentication process again to access the other system.
An attacker can take advantage of this arrangement by sending a packet to one system that appears to have come from a trusted system. Since the trusted relationship is in place, the targeted system may perform the requested task without authentication.
Since a reply will often be sent once a packet is received, the system that is being impersonated could interfere with the attack, since it would receive an acknowledgement for a request it never made.
The attacker will often initially launch a disk operating system (DoS) attack (such as a SYN flooding attack) to temporarily take out the spoofed system for the period of time that the attacker is exploiting the trusted relationship.
Once the attack is completed, the DoS attack on the spoofed system would be terminated, and the system administrator might never notice that the attack occurred.
Firewalls should also be configured to discard any packets from outside of the firewall that have From addresses indicating they originated from inside the network. This is a situation that should not occur normally and it indicates spoofing is being attempted.
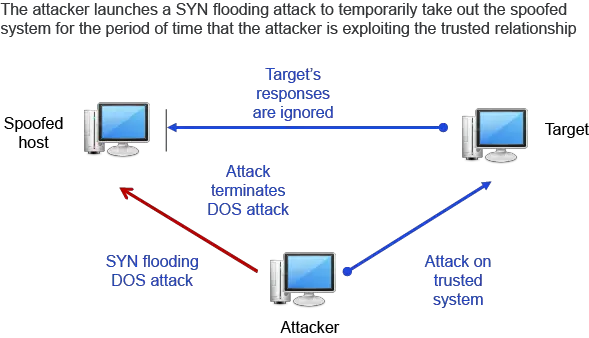
Figure 5 This illustration reflects an SYN flooding attack. The attacker launches a SYN flooding attack to temporarily take out the spoofed system for the period of time that the attacker is exploiting the trusted relationship.
Spoofing and Sequence Numbers
In the transmission control protocol (TCP) three-way handshake, two sets of sequence numbers are created. The first system chooses a sequence number to send with the original SYN packet. When the second host responds and sends its own SYN packet, it generates another sequence number.
The second host also sends an ACK packet in response to the first host’s SYN packet. The ACK packet includes the original sequence number incremented by 1. The original host system receives the SYN/ACK with both sequence numbers and then increments the second host’s sequence number by one and passes it back in an ACK packet response.
Spoofing attacks from inside a network are typically easier than attacks from outside a network because an attacker can more easily observe the traffic inside the network and can do a better job of formulating the necessary packets.
If the attacker is inside the network and can observe the traffic with which a target host responds the attacker can easily see the sequence number the system creates and can respond with the correct sequence number.
If the attacker is external to the network and the sequence number the target system generates is not observed, it is next to impossible for the attacker to provide the final ACK with the correct sequence number.
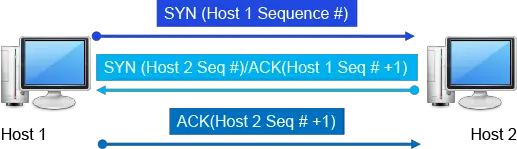
Figure 6 Spoofing and Sequence graphic illustrates the two host sequences described above.
Man-in-the-Middle Attack
When an attacker successfully inserts themselves between two other hosts’ communications by spoofing addresses, it is referred to as a man-in-the-middle attack.
A man-in-the-middle attack is usually accomplished by manipulating a router to alter the path of the traffic. The traffic is sent to the attacker rather than the intended target and then relayed on to the target host. This enables the attacker to observe the traffic from each target host in route and may even allow the attacker to modify or block certain messages.
Since all expected replies are received by the target hosts, it can appear to them that communications are occurring normally. If the data being intercepted from the target hosts is encrypted, the attacker may only be able to get a limited amount of information.
Review Figure 7 for an illustration of a Man-in-the-Middle Attack as described in this section.
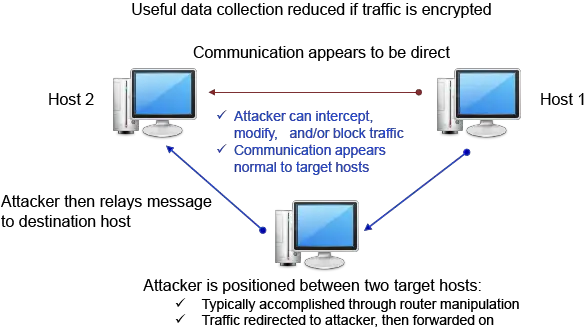
Figure 7 Illustration of Man-in-the-Middle Attack
Replay Attack
A replay attack occurs when an attacker captures a portion of a communication between two hosts and then retransmits the captured message at a later time. Replay attacks are often used to circumvent authentication mechanisms.
Systems can prevent falling victim to a replay attack by encrypting traffic, providing cryptographic authentication, and including a time stamp with each portion of the message. For illustration see Figure 8.
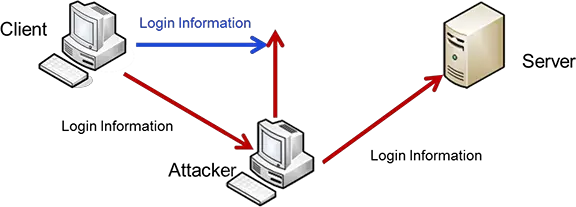
Figure 8 Replay Attack
TCP/IP Hijacking
Transmission Control Protocol/Internet Protocol (TCP/IP) hijacking and session hijacking are terms used to refer to the process of taking control of an already existing session between a client and a server.
The advantage to an attacker of hijacking over attempting to penetrate a computer system or network is that the attacker does not have to circumvent any authentication mechanisms.
To prevent the user from noticing anything unusual, the attacker may target the user’s system with a DoS attack, taking it down so that the user, and the system, will not notice the extra traffic that is taking place.
Hijack attacks generally are used against web and Telnet sessions. Refer to Figure 9 for an example of TCP/IP Hijacking.
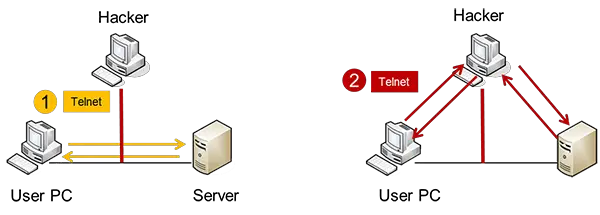
Figure 9 TCP/IP Hijacking: This graphic illustrates an attacker taking over an existing session and communicating between the sender and receiver.
Drive-by Download Attack
A drive-by download attack is accomplished by initiating downloads of malware, whether a user clicks it or not. Drive by downloads can initiate from a couple of different mechanisms.
It is possible for an ad that is rotated into content on a reputable site to contain a drive by download. Users do not have control over what ads are presented.
A second, more common method is a website that the user gets to either by mistyping a URL or by following a search link without being sure of what they are clicking for. Review Figure 10 for an illustration.
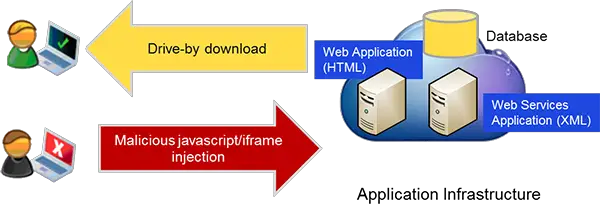
Figure 10 Drive-by Download Attack: Illustration depicts how a user inadvertently receives malware either from a legitimate site or malformed URL site.
Summary
It is important to be aware of the various types of potential threats that an attacker may launch against a network. In this lesson you learned about different types of network attacks and the use of assessment tools that can be applied to determine security threats and vulnerabilities to safeguard against attacks.
Network Attacks Key Takeaways
Understanding the various types of network and wireless attacks is crucial because these threats directly impact the security, availability, and integrity of systems and data in real-world applications. Denial-of-service attacks can disrupt business operations by making services unavailable to legitimate users, while spoofing and man-in-the-middle attacks compromise trust and confidentiality by impersonating users or intercepting sensitive information. Sniffing and replay attacks expose critical data, increasing the risk of unauthorized access. By recognizing these attack methods and the vulnerabilities they exploit, organizations can implement effective prevention techniques, such as firewalls, encryption, and timely patching, to protect their networks.