The article provides an overview of key concepts in network security, focusing on authentication, authorization, and various methods and protocols used to secure access to network resources. It covers user access strategies, password policies, and protocols such as PAP, CHAP, MS-CHAP, EAP, 802.1x, AAA, RADIUS, TACACS+, and Kerberos.
Lesson Objectives
By the end of this lesson, you will be able to:
- Explain how authentication and authorization affect network security.
- Compare and contrast user authentication method.
- Describe methods for providing network access security.
User Access and Authentication
Authentication has to do with verifying a user is who they say they are. It takes into account what the user has and what the user knows.
Defining a method for assigning usernames can be challenging and a network administrator must decide whether to present users with easy to remember usernames (i.e. first initial, last name) or more abstract usernames (i.e. employee id number).
The goal for username and passwords is to choose one that is not easily guessed. However, network administrators must consider the tradeoffs. Do they want the usernames to be hard to guess and hard for users to remember or easy to guess and easier for users to remember.
Complex username and password conventions may result in high volume helpdesk inquiries from account lockouts. Having a high number of account lockouts would be an undesired result, taking more human resources and time to address account lockouts issues.
A strong password is described as being:
- Eight or more characters
- Combinations of letters, numbers, and symbols
- Hard to guess
- Changed on a regular basis (30, 60, 90 day intervals)
Account lockout occurs is when a user unsuccessful attempts to access a system multiple times. This is a security feature to prevent hackers from trying an unlimited number of combinations and passwords to try to gain access to a network resource.
Having a high number of account lockouts would be an undesired result, taking more human resources and time to address account lockouts issues. Moreover, the more complex the username and password are, users who forget will add more volume to helpdesk resources.
Authorization
Authorization has to do with what the user is allowed to do on the network and what other networked systems a user can access.
It is common that authorization has to do with the role someone is placed in within an organization. An example would be a help desk associate should not be authorized to a file server or files in the legal department because it is not a function of his/her role.
Windows implements User-Level Security, where each user has an account and within that account a user rights are defined. An older form of authorization and access, is to assign password to a resource such as a printer or a server, this is called Share-Level Security.
Access Control Lists (ACLs) are commonly used within User-Level Security and on firewalls to determine whether a user, object, or traffic is allowed access to a resource.
Authentication
There are a few types of authentication methods which can be applied: multifactor authentication, two-factor authentication, or single sign on.
- Multifactor authentication combines what ‘an object knows’, ‘what an object has,’ and what an ‘object is,’ to determine whether or not access will be granted to a resource.
- Two – factor authentication requires that a user or system have two authentication methods to be granted access to a resource. For example, the military and other government offices use smart cards in conjunction with username and password information to grant user access to computer systems. However, two-factor authentication could be a fingerprint (biometric) and username and password or RSA key fob and retina scan (biometric) or any other two authentication methods.
- Single sign on is where with one successful logon, using a username and password, a user is authenticated to access multiple resources and systems. For instance, using an Apple ID, a user is able to check email, purchase applications from the App Store, and buy products using their phone for example. One logon, accesses a wide variety of resources. Microsoft also has single sign-on where user’s can access email, photos, documents, and the windows store using a Microsoft ID.
With company mergers and acquisitions, Network and Systems administrators often struggle to incorporate or merge data and resources from the acquired party.
Windows Active Directory Federation Service allows “trusts” to be set up where company “A” username and password will work to access company “B” data and resources even though they are on different domains.
Authentication Protocol
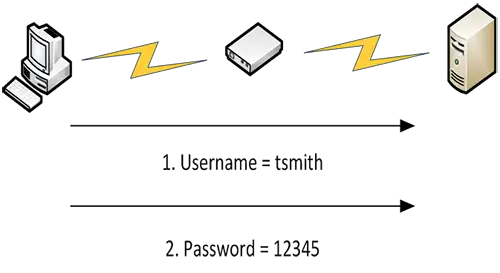
Password Authentication Protocol (PAP) sends data across a Point-to-Point Protocol (PPP) link, which is a Layer two protocol. Once the Point-to-Point protocol is set up between a client and the authentication server, PAP repeatedly sends the username and password in plain text until authenticated.
The authentication server compares the submitted data with the data it has stored in a database and if the username and password match, the user is authenticated.
Figure 1 Password Authentication Protocol (PAP) Process
Challenge Handshake Authentication Protocol
Challenge Handshake Authentication Protocol (CHAP) is more secure than PAP because the password is not sent in plain text; it is encrypted and sent along with a hash function supplied by the authentication server.
A hash function takes a string and uses a mathematical equation to produce a unique fixed length value as output.
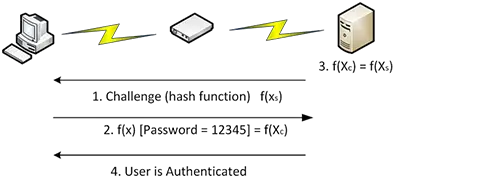
Figure 2 Challenge Handshake Authentication Protocol (CHAP) Process
Microsoft Challenge Handshake Authentication Protocol
Microsoft Challenge Handshake Authentication Protocol (MS-CHAP) is a Microsoft implementation of CHAP. Version 1 of CHAP and MS-CHAP have vulnerabilities.
If a hacker is eavesdropping on the network using a packet sniffer, they can capture the string of encrypted characters, hash function, with the password. They then have the ability to decrypt the string and obtain the user’s password.
MS-CHAP Version 2 uses stronger encryption and Mutual Authentication where both the client and the server authenticate one another using hash functions. This raises the security complexity of the protocol.
Extensible Authentication Protocol
Extensible Authentication Protocol (EAP) is most commonly used in wireless networks. EAP does not handle the encryption and authentication process, it facilitates this process, like a middle-man. The client and authenticator must be configured to send and receive EAP messages, however most modern operating systems support EAP. The EAP extends on the Point-to-Point protocol.
It is best to describe how EAP works from a wireless network perspective.
Like CHAP, EAP authentication is initiated from the authenticator, which in this case will be a wireless access point. EAP is adaptable in that it works with many authentication methods, like biometrics, smart cards, RSA tokens, and username and password combinations.
EAP is often used with older less secure encryption and authentication protocols, in an effort to make them more secure.
There are five steps that occur. See Figure 3 for example.
- The access point sends an EAP message to the client to verify itself and to establish the authentication type that will be used.
- The client computer returns the identity information that is requested by the access point and the access point forwards that information to an authentication server. The access point is the middle man.
- The access point will then send a request to the client to prove its identity, by authenticating, using a password or shared secret.
- The client will send that password or shared secret to the access point, which forwards that data to the authentication server for validation.
- The authentication server will then accept or reject the client request to join the wireless network.
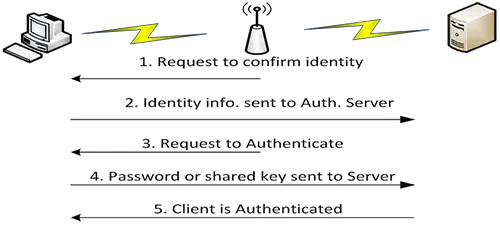
Figure 3 Extensible Authentication Protocol (EAP) Process
802.1x
802.1x is the IEEE standard, and along with EAP, requires the client to authenticate before a connection is granted. This standard is made up of three systems. The Supplicant is the client that is requesting network access.
The authenticator is the network object that the supplicant or client is trying to connect to, in order to gain network access. The authentication server processes request sent by the client and if the request is validated, access to the network is granted.
The feature that distinguishes this standard from others is that access is port based. A port on an access point or switch is opened to the client’s traffic only after the client is authenticated.
AAA Protocol
Authentication, Authorization, Accounting (AAA) protocols are commonly used in a centralized network security environment where users are first authenticated against a centrally managed database.
Based on the network privileges assigned to the authenticated user, they will either be allowed or denied access to network systems and resources. This is the authorization step. The user’s activity will then be tracked to determine network and resource usage, which is the accounting step.
RADIUS
RADIUS is popular for remote access to internal network resources. Authentication requests for various servers on the network may be directed to a RADIUS server freeing up resources on those servers to do other tasks. RADIUS is server based, uses user datagram protocol (UDP) and is highly scalable. An example is a virtual private network (VPN) server.
Terminal Access Controller Access Control System Plus
Terminal Access Controller Access Control System Plus (TACACS+) was developed to authenticate network equipment rather than users. It also allows the option to separate the authentication, authorization, and accounting roles and delegate another technique. For instance, instead of TACACS + using the AAA protocol for authenticating users, that role could be delegated to the Kerberos protocol. TACACS+ uses Cisco protocol, TCP, and network equipment based routers and WAPs for example.
Kerberos
Kerberos protocol was developed by Massachusetts Institute of Technology (MIT) and provides authentication for client/server applications. It can be used on UNIX and Windows platforms to verify the identity of clients and servers.
It provides a secure way to access an exchange of information between network systems by using private key encryption, also called Secret – Key Cryptography. Kerberos is used to guarantee privacy and data integrity.
The Kerberos protocol is made up of several components; The Principal, KDC, AS, Session key, Authenticator, TGS and TGT. These components create and describe the overall functionality of the Kerberos Protocol.
Figure 4 provides an example of how Kerberos works along with twelve steps outlined below.
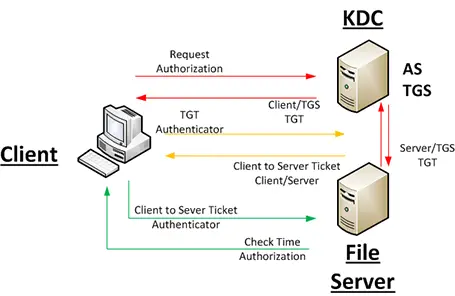
Figure 4 How Kerberos Works
The following steps outline how Kerberos works.
- Users and computer systems (i.e. Servers) on the network have private keys created by using a hash function. A user’s password for instance can be hashed; and that hash value is stored as the user’s private key. Servers also generate a private key and these keys are stored within the Authentication Service on the KDC server. The Authentication Server in the above diagram can be viewed as the KDC Server.
- A principal also referred to as a client or user, logs on to a workstation using his/her username and password. They are successfully authenticated on the workstation.
- The Principal requests a ticket in order to access the File Server.
- The Principal Username is sent to the KDC and verified.
- The AS running on the KDC server generates two new unique keys, referred to as session keys.
- One of the keys is issued to the Principal computer and the other to the KDC. A ticket/certificate is used to send this key information.
- The Ticket Granting Service (TGS) which is also running on the KDC server issues a Ticket-Granting Ticket (TGT), encrypted with the Principal Private Key.
- The Principal receives the encrypted TGT and decrypts the data.
- The Principal then creates a time stamp, referred to as the authenticator and encrypts the ticket with the session key. The Principal then sends the ticket and authenticator to TGS.
- The TGS then sends tickets to the server on behave of the Principal. This ticket contains the authenticator information and the session key established earlier.
- The File Server decrypts the ticket using its own key and decrypts the authenticator using its session key.
- The File Server verifies the Principal and access is granted.
Public Key Infrastructure
Public Key Infrastructure (PKI) is a cryptography system used for authentication and encryption. It requires a Certificate Authority commonly referred to as a CA.
The CA issues digital certificates which are used to identify an object (user, computer, and router. These certificates contain the Public key, encryption type, and other information to be compared with an object’s Private Key.
Network Security Key Takeaways
Network security is a vital component of computer networks.
- Authentication, authorization and encryption are ways that computer networks address network security.
- Remote access solutions can use CHAP, MS-CHAP, EAP, AAA, Kerberos, PKI and other protocols to secure communications with remote users.